The point where DORA and DMARC intersect

Quick Answer
DORA (Digital Operational Resilience Act) is a Europe-based framework explicitly designed to establish regulatory compliance for the finance sector. This act has been in force since January 2025. Though DORA and DMARC are not directly linked with each other, DMARC helps in DORA compliance by improving the email security posture.
Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
DORA (Digital Operational Resilience Act) is a Europe-based framework explicitly designed to establish regulatory compliance for the finance sector. This act has been in force since January 2025. Though DORA and DMARC are not directly linked with each other, DMARC helps in DORA compliance by improving the email security posture.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
For a complete overview, see our comprehensive DMARC guide.
DMARC is an email authentication protocol that empowers domain owners to instruct receiving mail servers on how to treat illegitimate emails sent from their domains. It helps reduce instances of phishing and spoofing.
The 7 chapters of DORA
DORA compliance is roughly broken down into seven chapters that help finance companies against Information Communication Technologies-related risk management, incident reporting, and operational resilience.
1. Subject matter, scope, and definitions
This chapter is all about knowing the purpose and scope of DORA. This primarily includes which kinds of entities, such as banks, investment firms, and insurance companies, are meant to be compliant with DORA.
2. ICT risk management
ICT risk management focuses on taking care of business continuity and establishing a proper, well-detailed incident response procedure.
3. ICT-related incident reporting
In this, obligations for reporting important ICT-related incidents are set. It explains how to report such incidents to competent authorities while also offering a way to determine the significance of the incident.
4. Digital operational resilience testing
The testing phase is all about ensuring that ICT systems are capable of handling and recovering from disruptions. This includes determining vulnerabilities, conducting penetration tests, and performing advanced threat-led penetration testing for critical systems.
5. Management of ICT third-party risk
This DORA chapter covers the risks of outsourcing ICT services. Financial firms must ensure third-party providers meet regulations and include these standards in contracts.
6. Information sharing arrangements
This chapter encourages you to foster cooperation and improve the overall cybersecurity situation of the entire financial sector.

7. Competent authorities and oversight framework
It defines the authority of regulators, allowing them to investigate, enforce fines, and implement corrective measures.
How do the DORA chapters intersect DMARC?
Here’s how each chapter is linked with DMARC and how these two come together to combat email-based menaces-
The second chapter
DMARC has a reporting mechanism that helps domain owners and administrators monitor email activities and detect unauthorized use of their domain for phishing and spoofing.
DMARC’s reporting mechanism provides domain owners with two types of reports:
- Aggregate reports (RUA): Summarize email authentication results across a period, showing sources sending emails on behalf of the domain.
- Forensic reports (RUF): Provide detailed failure reports for individual emails that fail DMARC authentication.
The third chapter
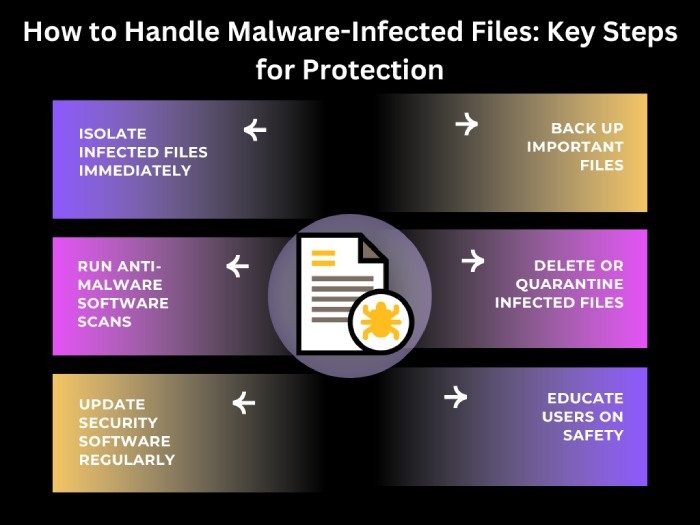
It’s common for threat actors to exploit domain vulnerabilities and send emails on behalf of brands. They manipulate targets into sharing sensitive details, downloading malware-infected files, transferring money, etc. However, if your domain is protected with DMARC, such emails will either be marked as spam or never reach the recipients’ inboxes.
The fourth chapter
DMARC users can identify and address fraudulent emails, helping to develop a robust cybersecurity strategy for financial organizations.
The fifth chapter
Setting p=quarantine or p=reject in your DMARC record ensures fraudulent emails are not getting placed in the primary inboxes of recipients. This way, the targets are less likely to engage with malicious emails and fall in the trap.
The sixth chapter
Implementing DMARC on all active and parked domains provides complete email protection, preventing phishing, spoofing, and ransomware attacks.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →